Linux Infrastructure Hardening and SIEM Orchestration#
Compliance status: 83%
Starting baseline: 26%
Framework: CIS Arch Linux Benchmark
Environment: Arch Linux security lab with Wazuh-based monitoring
1. Executive Summary#
This project documents the hardening of a newly deployed Arch Linux system using CIS-aligned controls and centralized monitoring through Wazuh. The goal was not only to raise the benchmark score, but to build a host that was easier to audit, harder to misuse, and capable of producing actionable security telemetry.
Over the course of the engagement, I remediated more than 100 configuration issues spanning identity management, filesystem protections, kernel behavior, and network exposure. The final system reached 83% CIS compliance and produced materially stronger audit coverage through auditd, Wazuh SCA, and policy-driven service restrictions.
2. Technical Stack#
- Operating system: Arch Linux
- Monitoring platform: Wazuh
4.14.4deployed in Docker - Instrumentation:
auditd,libpwquality - Hardening controls:
pam_pwquality,systemd,sysctl,visudo,ip6tables - Automation environment: Fish shell for repeatable remediation steps
3. The Monitoring Dashboard#
Wazuh served as the operational center for the project. It provided a consolidated view of benchmark findings, agent health, vulnerability data, and MITRE ATT&CK-aligned detections, which made it easier to validate each remediation step against a measurable control outcome.
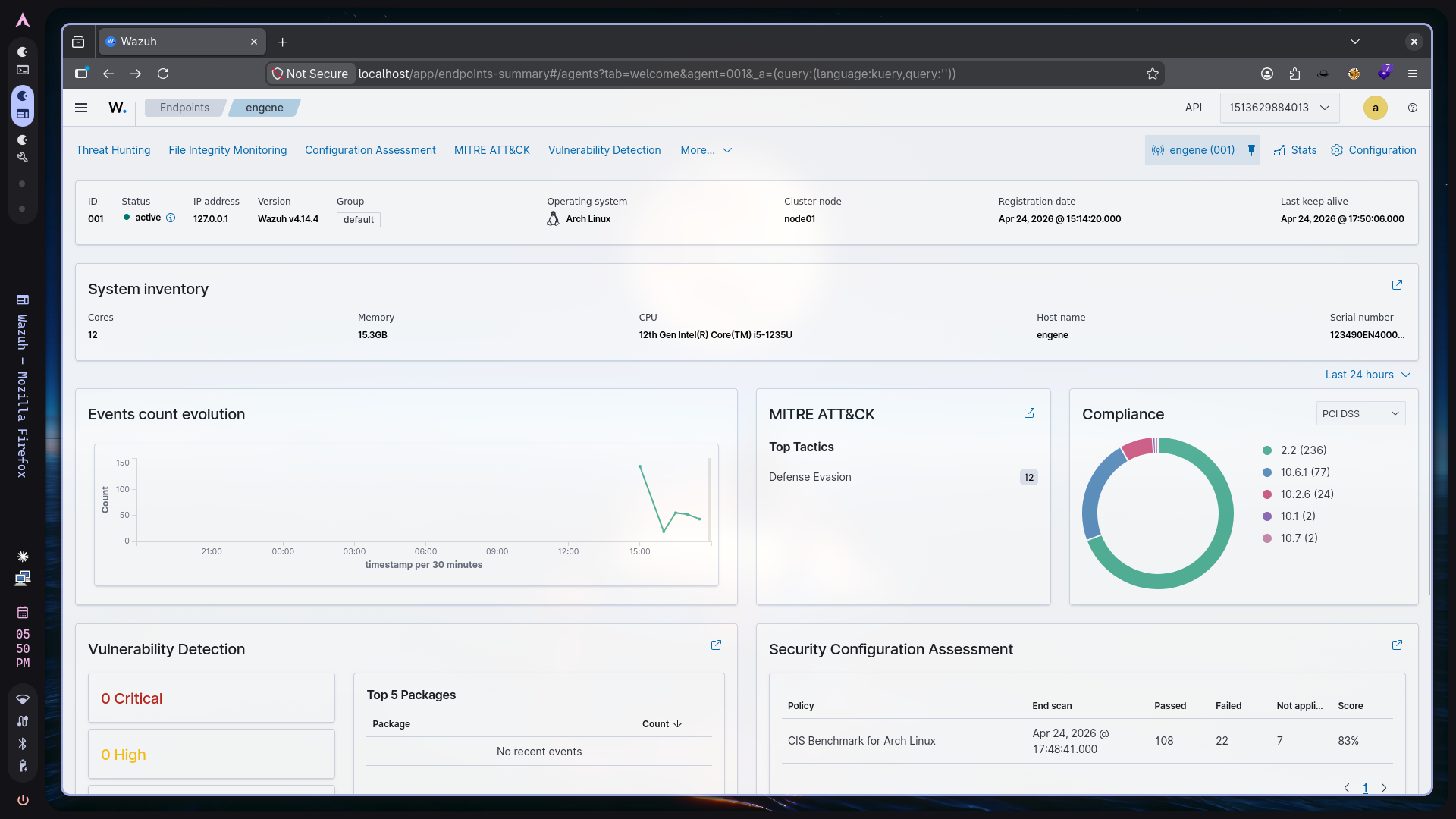 Figure 1. Wazuh dashboard showing the monitored Arch Linux endpoint and active security telemetry.
Figure 1. Wazuh dashboard showing the monitored Arch Linux endpoint and active security telemetry.
4. Implementation Phases#
Phase 1: Instrumentation & Baseline#
The first step was to deploy the Wazuh manager and enroll the Arch Linux host as an agent. Once the agent began reporting, the initial Security Configuration Assessment established a baseline score of 26%. Most failures were concentrated in authentication controls, service exposure, and auditability.
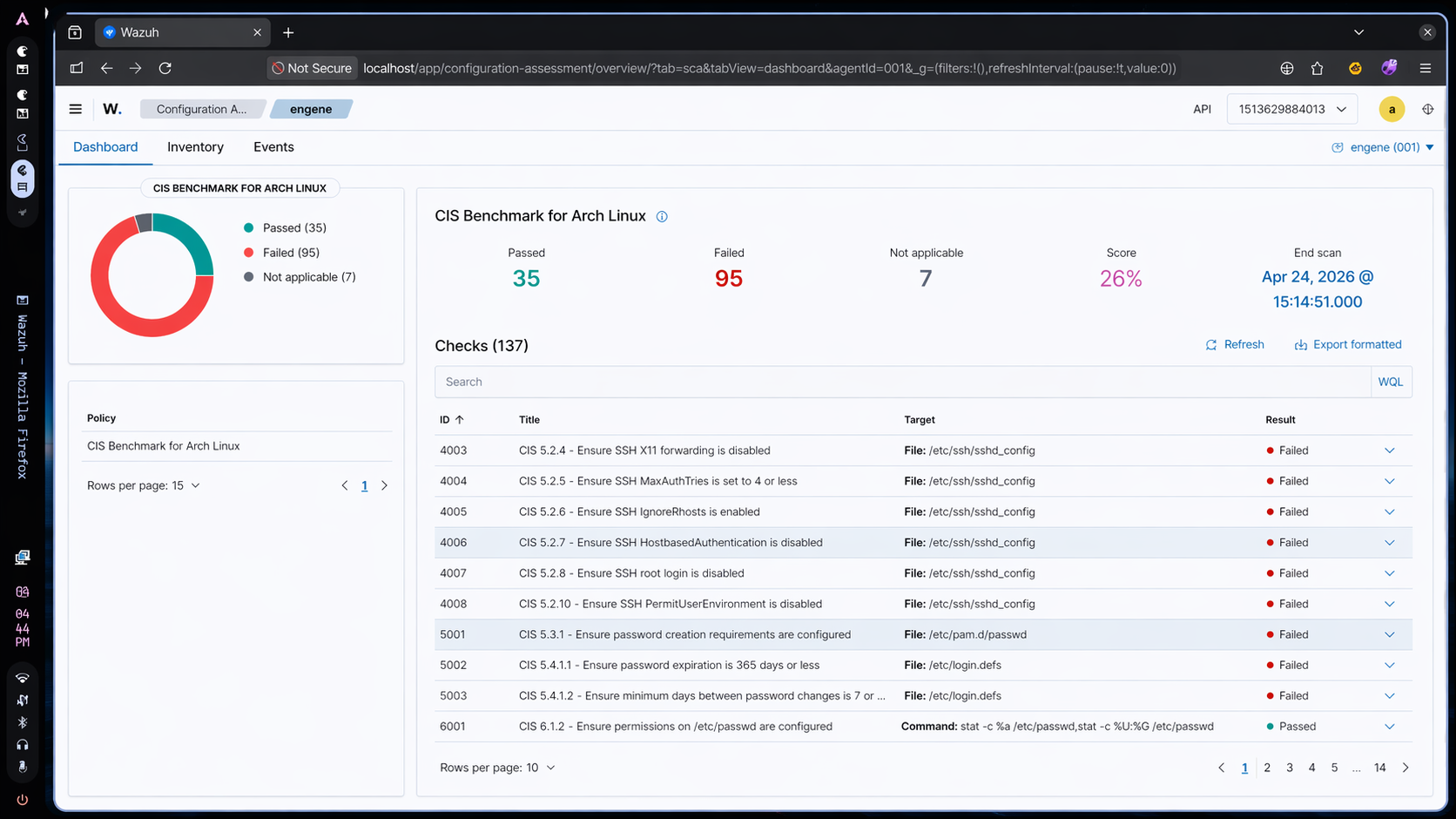 Figure 2. Initial CIS assessment showing low baseline compliance and multiple gaps in core host protections.
Figure 2. Initial CIS assessment showing low baseline compliance and multiple gaps in core host protections.
Phase 2: Remediation Sprints#
To keep the work structured, I grouped remediation into focused sprints based on control families rather than fixing findings one by one.
Sprint A: Identity and Access Management#
- Sudo hardening: Enabled
use_ptyand configured dedicatedsudologging to improve command accountability. - Privilege restriction: Limited
suaccess to thewheelgroup withpam_wheel.so. - Password policy: Enforced password aging and complexity requirements through
login.defsand related PAM controls.
Sprint B: Filesystem and Kernel Hardening#
- Mount restrictions: Applied
noexec,nosuid, andnodevon/tmp,/var/tmp, and/dev/shm. - Kernel module policy: Added
modproberules to disable unnecessary or risky filesystem modules and to block unauthorized USB storage support.
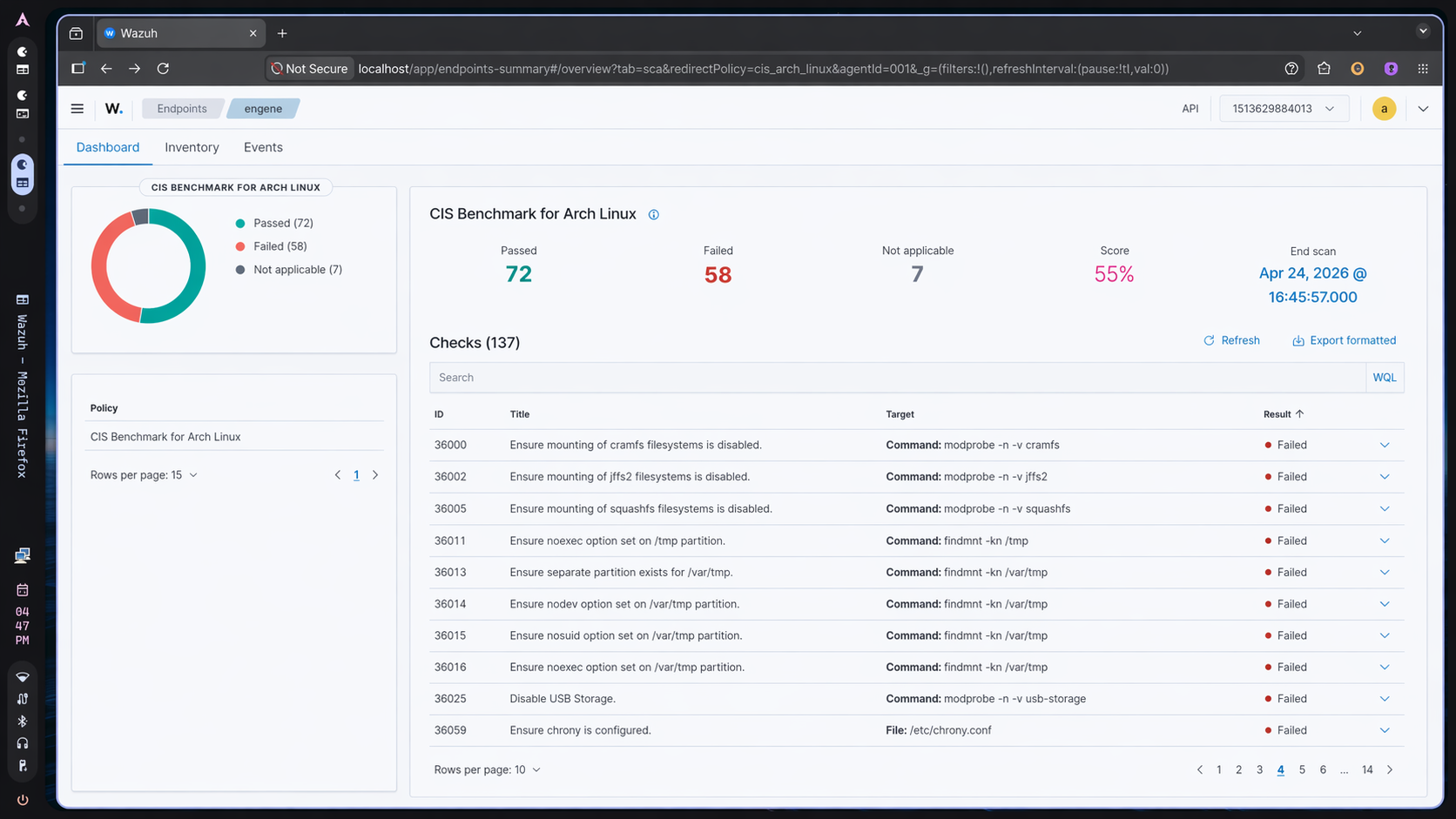 Figure 3. Mid-project assessment after initial filesystem, kernel, and service hardening raised compliance to 55%.
Figure 3. Mid-project assessment after initial filesystem, kernel, and service hardening raised compliance to 55%.
Sprint C: Network Surface Reduction#
- Service masking: Disabled and masked legacy services such as FTP, Telnet, SNMP, and HTTP where they were not required.
- Kernel network settings: Tightened
sysctlparameters to disable forwarding and reject unsafe redirect behavior.
Phase 3: Deep Telemetry & Auditing#
The final phase focused on depth of visibility. To address the more demanding CIS audit requirements, I expanded host-level telemetry with auditd and loaded more than 22,000 rules derived from the Neo23x0 baseline. That rule set captured high-value system events such as:
-k modulesfor unauthorized kernel module activity-k scopefor changes tosudoersand related privilege boundaries-k file_creationfor suspicious file creation attempts in restricted locations
5. Key Results#
- Compliance improvement: Increased the CIS score from
26%to83%, a gain of57percentage points. - Reduced attack surface: Removed or constrained common privilege escalation and lateral movement paths.
- Operational visibility: Established near real-time monitoring for host-level changes and audit events.
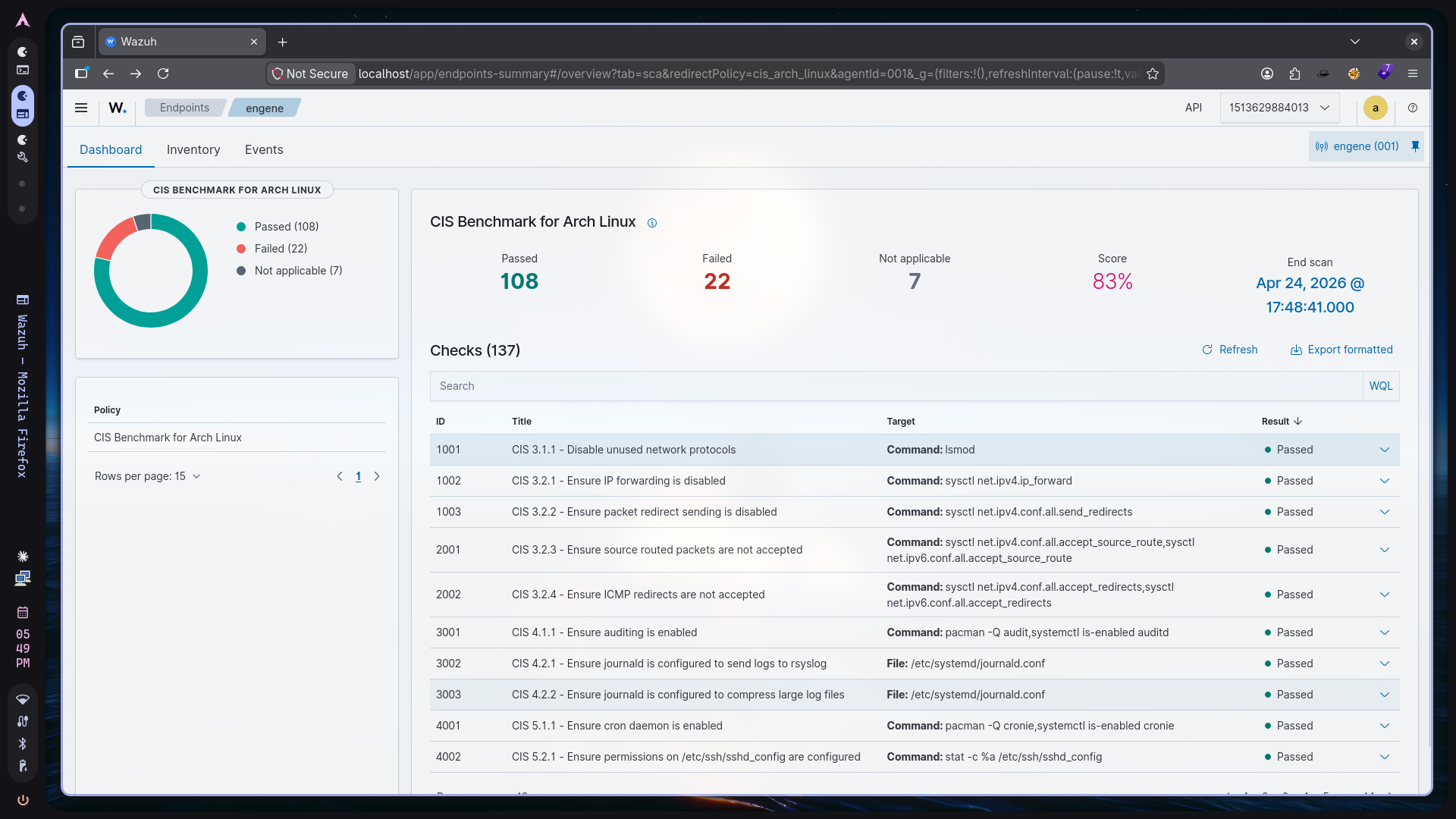 Figure 4. Final CIS assessment reflecting an 83% compliance score after remediation and audit expansion.
Figure 4. Final CIS assessment reflecting an 83% compliance score after remediation and audit expansion.
6. Lessons Learned#
- Minimal base systems still require strong control design: Arch Linux starts lean, but enterprise-grade hardening still depends on deliberate policy, logging, and service management.
- Benchmarking is most useful when paired with telemetry: Raising a score is helpful, but the more valuable outcome was the ability to observe and validate changes continuously through Wazuh and
auditd. - Automation matters: Using shell-based remediation reduced drift and made it easier to apply the same controls consistently during iterative testing.
7. Project Completion Checklist#
- Deploy Wazuh SIEM
- Agent Instrumentation
- Kernel Hardening
- Telemetry Enrichment
- CIS Benchmark Compliance (80%+)